To beat a hacker, think like a hacker!
Discover your Website and Network Vulnerabilities. Detect Microsoft Exchange RCE CVE-2021-28480 with our Network Vulnerability Scanner.
Common Questions
See some common questions and answers below, or call us at +2349099425904, +2348180640370, +447731572897
- What is a penetration test?
A penetration test, also known as a “pen test” is a method for evaluating the effectiveness of an organization’s security controls.
- What are the goals of a penetration test?
Goals of a penetration test vary greatly based on the scope of review. Generally speaking, the goal of a penetration test is to validate the effectiveness of security controls designed to protect the system or assets being protected.
- Why should we have a penetration test performed?
A Penetration test should be performed for a variety of reasons. Some of the more common reasons why companies perform network penetration tests include:
- Most relevant regulatory standards require penetration tests are performed.
- Penetration testing can identify vulnerabilities inadvertently introduced during changes to the environment, such as a major upgrade or system reconfiguration.
- Penetration testing can be integrated into the QA process of the Software Development Life Cycle to prevent security bugs from entering into production systems.
- Organizations, especially those acting as data custodians, are being required to have testing performed by their customers.
- Penetration testing can demonstrate a commitment to security from a customer perspective and provide an attestation that their assets or services are being managed securely.
- Penetration testing is a common requirement for internal due diligence as part of ongoing efforts to manage threats, vulnerabilities, and risks to an organization. Results can be used as input into an on-going Risk Management process.
- Penetration testing allows companies to assess the security controls of potential acquisition targets. Most organizations preparing to acquire an organization seek insights into the vulnerabilities they may introduce in doing so and plan for the costs they may be incurring to remediate.
- To support a breach investigation, penetration testing may tell an organization where the other vulnerabilities may exist in order to have a comprehensive response to the incident.
- Penetration testing allows companies to proactively assess for emerging or newly discovered vulnerabilities that were not known or have not yet been widely published.
- Penetration testing serves as an aid to development teams who are writing new web applications. Many development lifecycles include penetration testing at key stages of the process.
- Correcting flaws is typically less costly the earlier in the development lifecycle that they are discovered. Additional testing prior to go-live on a production-ready build can identify any remaining issues that might require attention before loading users on the application.
- What are typical costs for a penetration test?
The cost of penetration testing varies greatly.
A number of factors are used to determine pen test pricing including, but not limited to the scope of the project, the size of the environment, the number of systems, and the frequency of testing. It is critical to have a detailed scoping meeting to produce a very clear understanding of the needs and develop a statement of work prior to engaging in any penetration test.
- How much experience do you have performing penetration testing?
Our engineers have thousands of hours of penetration testing experience, and decades of security background.
- How much time is needed to perform a typical penetration test?
Adequate time should be reserved in advance of a penetration test for planning activities. Additional time should be allocated after testing for report development and subsequent review meetings including remediation discussions. The entire effort varies greatly based on the size and complexity of the network penetration test. The larger or more complex the environment is, the more effort is required. The duration of the test, however, is very controllable. The duration of the test should be compressed to ensure a good, representative view of the environment at a given point in time.
Generally speaking, four to six weeks is a good estimate for the duration of the entire engagement from planning through final delivery.
- My customer wants to see the results of our penetration test. Should I share the penetration test report with outside parties?
It is not a good idea to send results outside of your company; a penetration test report contains extremely sensitive information that is highly confidential and should only be made available to trusted internal resources on a “need-to-know” basis. Sharing detailed reports with external individuals is not recommended. Once the penetration test report is shared with an external party, control over its distribution is difficult to guarantee. A penetration test report can be a roadmap to an organization’s vulnerabilities and should not be distributed outside unless absolutely necessary.
A network penetration tester should provide a summary version of the report that details scope, approach, qualifications and categorical results. This summary report is more appropriate for an organization to share. It is common to include summary remediation plans if applicable but ultimately, the third party needs to receive documentation that gives them comfort that there is a mature, ongoing testing program that is proactively assessing the environment, and that key findings are being appropriately addressed. Providing the external party specific test details could present a significant security risk. A summary deliverable can be provided to third parties that provides insight into the testing without revealing sensitive details.
- When do you need a penetration test?
- Prior to contracting for breach insurance
- Notice viruses, malware, spyware on workstations
- After implementing significant changes in website or network
- Unauthorized traffic on network noted
- Security audit for HIPAA or PCI-DSS
- After installing new software or other upgrades
- Prior to submission of application for breach insurance
- If you store valuable data and have never had one
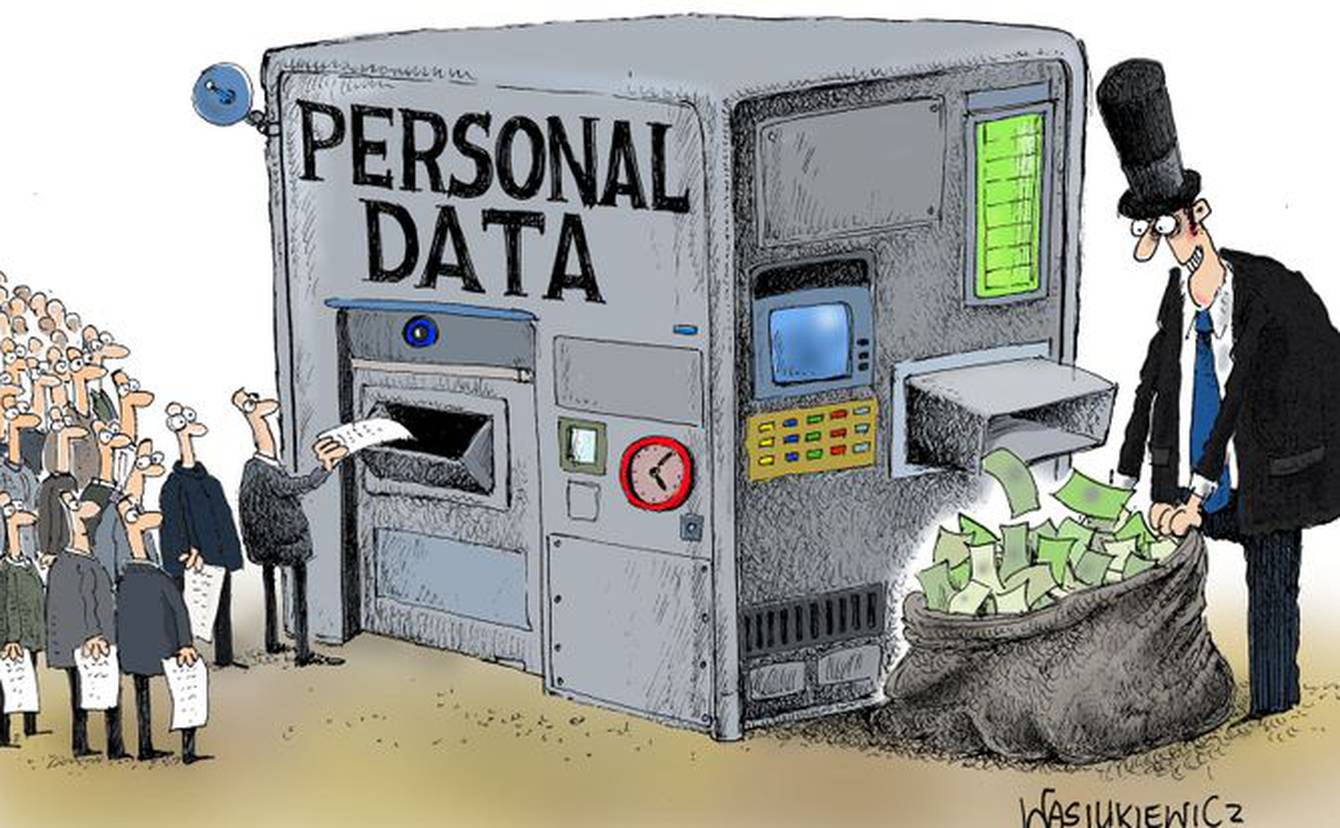
- My Data is stored in the cloud. Why do I need a Penetration test?
- Software, particularly custom software, is almost always filled with security holes and vulnerabilities. Your cloud provider has no control over your software
- Your corporate environment devices - all-in-one printers, wireless servers, laptops, workstations, modems, are vulnerable and testing is crucial for this environment